Weapon Tracking System with Chain of Custody Management
Introduction
Chain of custody (CoC) management is a critical component of weapon tracking systems that ensures complete accountability for every firearm and piece of equipment in an armory. It provides a complete trail of custody, control, transfer, and disposition of weapons throughout their lifecycle. For law enforcement agencies, military organizations, correction departments, border units, and private security firms, maintaining an unbroken chain of custody is not just a best practice—it is a legal and operational necessity.

What is Chain of Custody Management?
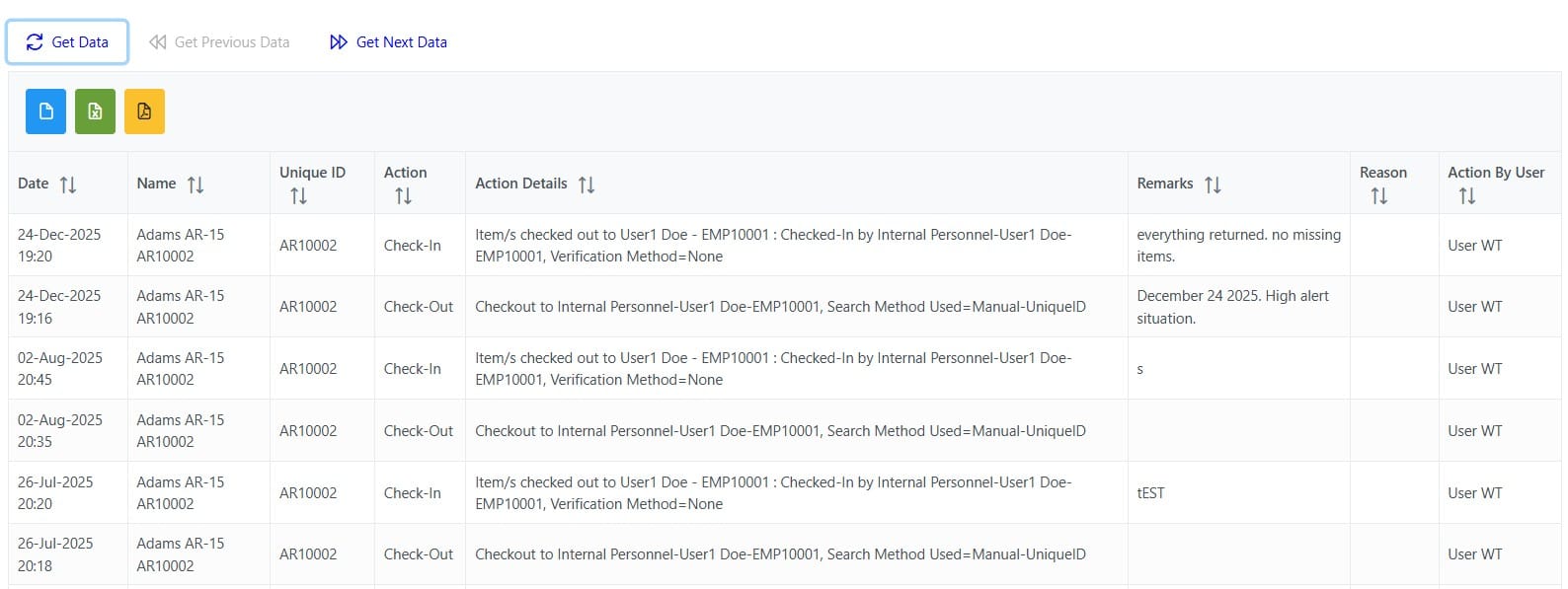
Chain of custody management in weapon tracking refers to the chronological documentation and paper trail that records the sequence of custody, control, transfer, analysis, and disposition of weapons and related equipment. In case of weapon tracking systems, it is complete audit trail of transactions that mirrors physical process. This audit trail can be printed as and when needed. The audit trail is tamper-proof and cannot be edited to maintain integrity of records. It ensures that every transaction is accurately recorded and traceable. This comprehensive record ensures that:
- Every transaction is recorded: From issue to return, every weapon movement is recorded
- Accountability is maintained: Clear identification of who has custody at all times
- Integrity is preserved: Evidence of proper handling and security protocols
- Compliance is ensured: Meeting regulatory and organizational requirements
- Investigations are supported: Complete audit trails for incident investigations
Effective chain of custody management is essential for preventing unauthorized access, ensuring legal accountability, maintaining regulatory compliance, mitigating risks, and supporting operational integrity. It is the foundation upon which secure and responsible weapon tracking systems are built. In GOBO Systems' RFID Weapon Tracking System, we have designed our solution with chain of custody management at its core, providing the tools and features necessary to maintain an unbroken custody trail and ensure complete accountability for every weapon in your inventory.
What is the Importance of Chain of Custody Management?
Chain of custody management is the backbone of effective weapon tracking systems, providing an unbroken record of who has handled each weapon, when, and for what purpose. This meticulous documentation or audit trails is not just a mere requirement—it is a critical safeguard that ensures accountability, security, and compliance in critical and sensitive environments.
- Enhanced Security: Prevents unauthorized access, theft, or misuse by maintaining a clear record of weapon movements and custody transfers
- Legal Accountability: Provides irrefutable evidence in investigations, court proceedings, or incident reviews, demonstrating proper handling protocols
- Regulatory Compliance: Meets stringent requirements from law enforcement standards, military regulations, and government oversight bodies
- Risk Mitigation: Identifies potential security gaps early and enables rapid response to discrepancies or anomalies
- Operational Integrity: Builds trust with stakeholders by proving responsible stewardship of dangerous equipment
- Incident Response: Facilitates thorough investigations by providing complete historical records of weapon custody and usage
What are Common Challenges in Chain of Custody Management?
Manual Process Vulnerabilities
Traditional paper-based systems face several challenges:
- Human error in documentation: Human mistakes can lead to inaccurate or incomplete records
- Lost or damaged records: Physical documents are susceptible to loss, damage, or tampering
- Time-consuming reconciliation processes: Manual cross-checking of records is labor-intensive
- Difficulty in retrieving historical data: Searching through paper files is slow and inefficient
- Lack of real-time visibility: Searching through paper files delays getting proper & accurate information about weapons and associated items. It hinders timely decision-making
Multi-Location Operations
Organizations with multiple facilities face more challenges in maintaing chain of custody integrity across locations:
- Inter-facility transfers and coordination: Such transfers require careful planning and communication to maintain chain of custody integrity across locations. In paper based process, many times people face challenges in tracking and documenting these transfers accurately. It is due to either paucity of time or lack of standardized procedures or inadequate training.
- Maintaining consistent procedures across locations: Ensuring uniformity in chain of custody practices across multiple sites is crucial for operational integrity. Without online centralized systems, maintaining consistency across locations is challenging. It can lead to discrepancies and inefficiencies.
- Centralized visibility and reporting: Lack of centralized systems hinders comprehensive view of weapon movements and custody status across all locations. GOBO Systems' Weapon Tracking System provides centralized visibility and reporting capabilities.
- Synchronization of distributed systems: Coordinating data across different systems and locations is essential for accurate and timely information. It is extremely difficult with manual processes to synchronize data across locations.
Temporary Transfers
It's important to note that short-term custody transfers require special attention:
- Training exercises with multiple participants: Ensuring accurate tracking and documentation during training exercises is crucial for accountability.
- Maintenance and repair activities: Proper documentation during maintenance and repair activities helps maintain chain of custody integrity.
- Inter-agency collaborations: Coordinating custody transfers between agencies requires clear communication and documentation.
- Emergency response situations: Rapid response scenarios necessitate efficient tracking and documentation to ensure accountability.
Key Components of Chain of Custody Management
1. Initial Documentation
The chain of custody begins the moment a weapon enters the inventory system:
- Detailed weapon identification (serial number, make, model, type, butt)
- Internal Asset ID assignment
- Physical inpsection of weapon and documentation
- Photographic evidence if needed and unique identifiers verification with documents
- RFID tag/Barcode/QRCode assignment for automated tracking
- Initial ownership assignment and authorization
2. Transfer Documentation
Every time a weapon changes hands, comprehensive records must be maintained:
- Date and time of transfer
- Identity of person/armorer performing change of custody
- Identity of person receiving custody of weapon or associated equipment
- Purpose of transfer of custody (training, patrol, out of country duty, maintenance, etc.)
- Expected return date and conditions
- Digital signatures or biometric authentication of armorer and personnel receiving custody
3. Continuous Monitoring
Modern weapon tracking systems provide real-time custody monitoring:
- RFID with GPS/GSM technology if deployed together for automatic location tracking
- Access control integration for secure storage areas
- Alert systems for unauthorized movements
- Scheduled check-in/check-out verification
- Overdue return notifications
- Maintenance and Inspection tracking and history
- Incident reporting and investigation tracking
- Exception and Alert Management for overdue items, unauthorized possessions, missing weapons, inventory mismatches, expired certifications
Technology Solutions for Chain of Custody - Managing Chain of Custody Electronically
RFID Weapon Tracking Systems
Radio Frequency Identification (RFID) technology has revolutionized chain of custody management by providing:
- Automated tracking: Passive monitoring without manual scanning
- Real-time visibility: Instant location and custody status updates
- Reduced errors: Elimination of manual data entry mistakes
- Faster audits: Complete inventory verification in minutes
- Enhanced security: Immediate alerts for unauthorized system access or unauthorized exit of weapons
Biometric Authentication
Integrating biometric verification ensures that custody transfers are secure and verifiable:
- Fingerprint recognition for weapon checkout/check-in
- Facial recognition at access points
- Multi-factor authentication for high-security items
- Non-repudiation of custody transfers

Digital Signatures for Custody Transfers
Integrating digital signature pads to capture signatures ensures that custody transfers are secure and verifiable:
- Digital signatures for weapon checkouts by personnel receiving custody
- Digital signature capture for check-ins from armorers who have received the custody of weapons

Mobile Solutions
Mobile applications extend chain of custody capabilities to the field:
- Remote check-out/check-in functionality
- GPS location tracking for field operations
- Digital signature capture
- Real-time synchronization with central database
- Offline capability with automatic sync when connected

Best Practices for Chain of Custody Management
1. Establish Clear Protocols
- Define standard operating procedures for all custody transfers
- Create role-based access controls and authorization levels
- Implement mandatory training for all personnel
- Document exceptions and emergency procedures - in what circumstances they apply and how to handle them.
2. Maintain Complete Documentation
- Record every interaction with weapons. Complete item history should be maintained. Use RFID Weapon Tracking Systems for accurate tracking.
- Include maintenance, cleaning, test firing and inspection activities
- Document all system access and modifications. There should be a clear audit trail for every change made.
- Preserve records according to regulatory requirements. Ensure secure storage and controlled access to sensitive information.
- Don't allow editing of historical records to maintain data integrity.
3. Regular Audits and Reconciliation
- Conduct scheduled physical inventory counts. Maintain accurate records of all counts and discrepancies in RFID Weapon Tracking Systems.
- Reconcile system records with physical assets
- Investigate and document any discrepancies immediately
- Perform surprise audits to verify compliance
4. Implement Redundancy and Backup
- Maintain multiple backup copies of system data and store at secure place
- Use cloud-based systems for data redundancy
- Implement disaster recovery procedures
- Ensure system uptime and availability
Legal and Compliance Considerations
Chain of custody documentation serves critical legal purposes:
- Evidence admissibility: Proper custody records ensure weapons used in incidents can be verified
- Regulatory compliance: Meeting federal, state, and local requirements
- Liability protection: Demonstrating due diligence in weapon management
- Audit readiness: Prepared documentation for inspections and reviews
- Investigation support: Complete records for internal and external investigations
Benefits of Automated Chain of Custody Systems
Enhanced Accountability
- Clear responsibility at every stage
- Automated alerts for overdue returns
- Comprehensive audit trails
- Real-time custody status visibility
Improved Security
- Immediate detection of unauthorized access
- Reduced opportunity for theft or misappropriation
- Enhanced physical security integration
- Tamper-proof records
Operational Efficiency
- Faster check-out/check-in processes
- Reduced administrative burden
- Quick retrieval of custody history
- Streamlined audit procedures
Risk Mitigation
- Early detection of compliance issues
- Reduced liability exposure
- Better incident investigation capabilities
- Improved regulatory compliance
Why GOBO Systems for Chain of Custody Management?
GOBO RFID weapon tracking system provides comprehensive weapon tracking solutions designed to maintain unbroken chain of custody records and ensure complete accountability. Our deep expertise in armory management, combined with advanced RFID technology, makes us the trusted partner for organizations requiring mission-critical custody tracking systems.
Custody-Focused Design
Our RFID weapon tracking system is built with chain of custody at its core. Every feature is designed to maintain complete custody documentation—from automated transfer records and biometric authentication to real-time monitoring and comprehensive audit trails. We understand what custody integrity requires and ensure your system delivers it.
Complete Custody Framework
Our RFID weapon tracking system provides end-to-end custody management covering weapons, ammunition, accessories, and all transfer activities. Our integrated platform eliminates custody gaps, ensures consistent documentation across all operations, and creates tamper-proof custody trails that meet the strictest regulatory requirements.
Real-Time Custody Visibility and Alerts
Our system delivers instant visibility into custody status, transfer history, and compliance issues. Real-time dashboards, automated alerts for overdue returns, and exception reporting enable proactive custody management instead of reactive problem-solving. Identify and resolve custody issues before they become compliance problems.
Our Proven Experience of working with Law Enforcement, Military, and Security Organizations
GOBO Systems has helped law enforcement agencies, military installations, and security organizations maintain impeccable chain of custody records. Our clients have been using the systems for years without any issues with chain of custody, reporting zero custody breaks, faster investigations, and improved confidence in their accountability systems. We have deep understanding of the unique challenges and requirements of custody management in these critical environments, and our solutions are tailored to meet those needs effectively.
Comprehensive Implementation Support
We provide complete implementation services including requirements analysis, system setup & configuration, RFID tagging, user training, process definition & implementation, and ongoing support. Our team works closely with your team to ensure smooth deployment and operational excellence.
Regulatory Compliance Expertise
Our solutions address specific regulatory requirements for chain of custody documentation, transfer protocols, and audit trail standards mandated by law enforcement standards, military regulations, and government compliance frameworks.
Maintain Unbroken Chain of Custody with GOBO Systems
Learn how our RFID Weapon Tracking System ensures complete chain of custody documentation, or contact us to discuss your custody management needs.
Conclusion
Effective chain of custody management is fundamental to secure and accountable weapon tracking operations. Modern RFID Weapon Tracking System from GOBO Systems provides the automation, accuracy, and security necessary to maintain an unbroken chain of custody while improving operational efficiency. By implementing comprehensive chain of custody protocols supported by advanced technology, organizations can ensure regulatory compliance, enhance security, and maintain the trust of their stakeholders.
The investment in automated chain of custody management not only protects against liability and security risks but also demonstrates a commitment to professional standards and public safety. As weapon tracking requirements continue to evolve, organizations that prioritize chain of custody excellence will be better positioned to meet future challenges and maintain operational integrity.
FAQ-Frequently Asked Questions
Learn More
Want to learn more about maintaining chain of custody in your armory? Visit our Weapon Tracking System page or contact us for a consultation.